Remote patient monitoring (RPM) programs handle protected health information (PHI) at every layer: connected medical devices in patient homes, cellular and Bluetooth transmission paths, cloud infrastructure, EHR integrations, and care team workflows. Each layer is a compliance obligation under the HIPAA Security Rule, an FDA cybersecurity expectation if the device is regulated, and a real attack surface. The Change Healthcare breach in February 2024 (192.7 million records, the largest healthcare data breach in world history) reset the threat baseline for healthcare data security, and the regulatory bar has been rising since.
This guide covers HIPAA RPM compliance under the Security Rule (including the 2024 OCR Notice of Proposed Rulemaking expected to finalize in 2026), FDA cybersecurity requirements for RPM devices and software as of the March 2026 premarket guidance update, device-specific security considerations for BLE and cellular RPM hardware, common RPM-specific threat patterns, and how Mindbowser’s PHISecure compliance platform addresses these requirements on AWS.
The Data Landscape of RPM
Remote Patient Monitoring (RPM) systems collect various data types to monitor patients’ health remotely. These include-
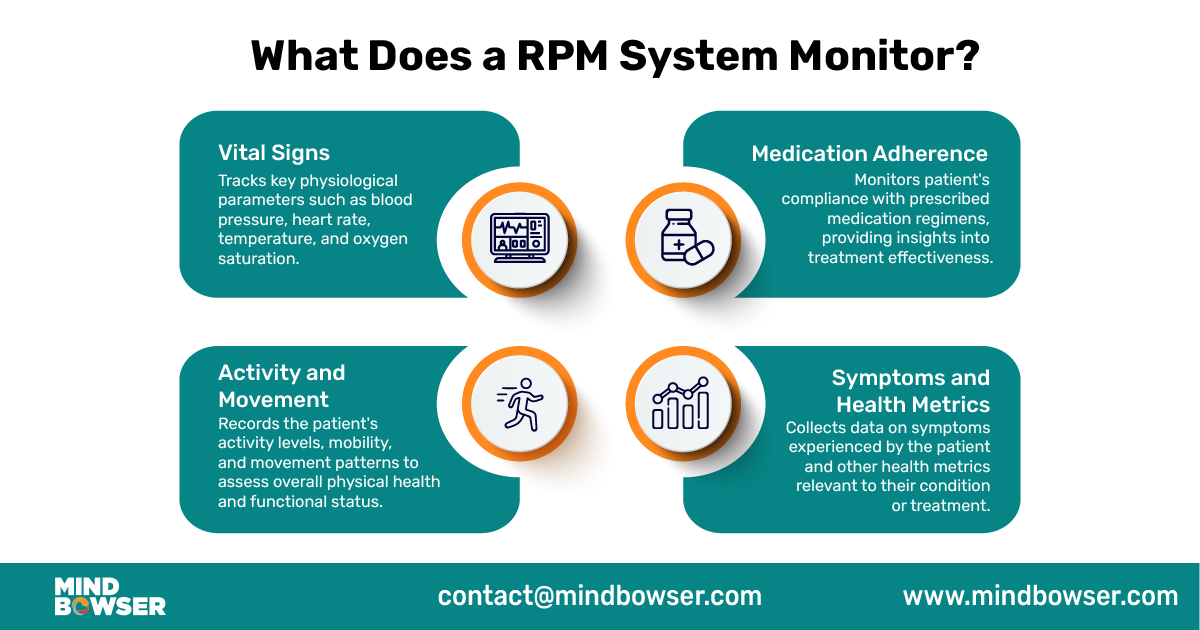
Vital Signs
RPM systems capture vital signs such as heart rate, blood pressure, oxygen levels, and temperature, which are highly sensitive and directly impact clinical decisions. This data flows from devices to apps and cloud systems, creating multiple points where security risks can occur. Without proper encryption and access controls, vital signs data can be exposed or misused.
Medication Adherence
RPM systems track patients’ medication adherence by recording when medications are taken or missed. Medication data helps healthcare providers ensure patients are following their prescribed treatment plans and can intervene if medication non-adherence is detected.
Symptoms and Health Metrics
RPM systems allow patients to report symptoms or provide other health-related information, such as pain levels, glucose levels for diabetic patients, or weight measurements for patients with heart conditions. Monitoring these metrics helps healthcare providers assess patients’ health status and adjust treatment plans accordingly.
Activity and Movement
Some RPM systems include activity trackers or motion sensors to monitor patients’ physical activity and movement patterns. This data can provide insights into patients’ mobility, exercise habits, and overall well-being.
Overall, RPM systems collect diverse data types to monitor patients’ health remotely and provide valuable insights to healthcare providers. However, ensuring data security in RPM is crucial to protect patients’ privacy and maintain trust in remote monitoring technologies.
Related read: Automated Remote Patient Monitoring: A Complete Guide for Healthcare Providers
Why Data Security Matters in RPM
RPM systems collect and transmit sensitive patient data in real-time. Without proper data security in RPM, there’s a significant risk of unauthorized access or RPM security threats. In the event of an RPM data breach, providers may face regulatory penalties and loss of trust.
Patient Trust and Confidence
Data security in healthcare is very important in the healthcare ecosystem. Breaches can significantly impact patient trust and confidence in healthcare providers and technology companies. When patients entrust their health information to RPM systems, they expect it to be kept secure and confidential. However, in case of data breach , it can lead to concerns about the safety and privacy of sensitive health data.
Patients may to participate in RPM if they fear their data is not adequately protected. This reluctance to engage with RPM systems can affect healthcare providers’ ability to monitor patients remotely and deliver timely interventions, ultimately impacting patient care outcomes.
Regulatory Compliance
HIPAA is a key regulatory framework in the United States that emphasizes data security in healthcare. HIPAA establishes standards and requirements for protecting the privacy and security of individually identifiable health information, including data collected through RPM systems. Healthcare providers and technology companies must comply with HIPAA regulations to ensure patient data security and privacy.
In addition to HIPAA, other relevant data privacy regulations include the General Data Protection Regulation (GDPR) in the European Union. Healthcare organizations, especially those working within the EU or dealing with EU residents’ data, must follow the GDPR’s guidelines. These rules outline how personal data, including health-related information, should be collected, processed, and protected. Compliance with GDPR requirements ensures patient data privacy, builds trust, and meets regulatory standards.
FDA Cybersecurity Requirements for RPM Devices and Software
If your RPM platform includes FDA-regulated medical devices (most BP cuffs, glucometers, pulse oximeters, and continuous monitors fall here), the FDA cybersecurity requirements apply directly. The bar moved meaningfully in 2026.
Section 524B of the Federal Food, Drug, and Cosmetic Act (added by the PATCH Act in March 2023) establishes statutory cybersecurity requirements for “cyber devices” submitted for FDA premarket review. The FDA’s premarket submission cybersecurity guidance was finalized in September 2023, refreshed in June 2025, and updated again in March 2026. Manufacturers must meet the updated standards by February 2, 2026.
Required premarket submission elements (March 2026 guidance):
- Security Risk Management Report documenting threat modeling, secure design decisions, and residual risks
- Software Bill of Materials (SBOM) listing every third-party and open-source software component, with version detail and known vulnerability mapping
- Detailed architecture views that allow FDA reviewers to assess exploitability across device, network, and cloud boundaries
- Penetration testing evidence with findings and remediation
- Postmarket cybersecurity management plan, including vulnerability disclosure and patch management commitments
The FDA expects threat modeling, secure design, and penetration testing to be applied across the full device lifecycle, not just at submission. Postmarket vulnerabilities discovered after market entry must be tracked, disclosed, and patched on a defined cadence.
What this means for RPM programs: if you’re building or selecting RPM hardware, verify with the manufacturer that they have a current Security Risk Management Report and SBOM available, and that postmarket patch management is in place. Devices missing these are increasingly likely to fail health system procurement reviews.
Securing Data in RPM: Responsibilities of IT Providers
Regulatory frameworks like HIPAA and FDA guidelines are central to data security in healthcare, particularly for remote patient monitoring. Robust encryption, secure cloud infrastructure, and role-based access controls are critical to reducing the risk of an RPM data breach.
Data Encryption
Encryption of data is important in securing patient information in remote patient monitoring (RPM) systems. It involves scrambling data using complex algorithms during transmission and storage, rendering it unreadable to unauthorized parties without a decryption key. This ensures that the data remains protected from being accessed or deciphered.
Common encryption standards used in healthcare, such as the Advanced Encryption Standard (AES-256), provide strong cryptographic protection for sensitive health information. AES-256 encrypts data with a 256-bit key, making it highly resistant to brute-force attacks and unauthorized access.
Access Control
Access control is another crucial aspect of securing patient data in RPM systems. It involves restricting access to patient data based on job duties and the principle of least privilege, ensuring that only authorized personnel can access specific information.
Multi-factor authentication (MFA) adds an extra layer of security by requiring users to provide multiple forms of identification, such as passwords, biometric verification, or one-time codes, to access patient data. This helps prevent unauthorized access, even if login credentials are compromised.
Data Storage and Transmission Security
Secure storage practices are essential to protect patient data from unauthorized access or breaches. IT solution providers should implement secure storage mechanisms, such as encrypted databases or secure cloud storage, to safeguard patient data at rest. Regular backups and data redundancy measures ensure data availability and integrity in system failures or disasters.
For data transmission, IT solution providers should use secure data transfer protocols, such as Transport Layer Security (TLS) or Secure Socket Layer (SSL), to encrypt data during transit between RPM devices, servers, and healthcare providers’ systems. These protocols establish secure communication channels, preventing interception or tampering of patient data during transmission.
By prioritizing data encryption, access control, and secure storage and transmission practices, IT solution providers can fulfill their responsibilities in securing patient data in remote patient monitoring systems. These measures protect sensitive health information and improve patient trust and confidence in RPM technologies.
Related Read- Securing Healthcare: The Critical Role of Data Security
HIPAA RPM Compliance: Security Rule Safeguards and What’s Changing in 2026
HIPAA RPM compliance rests on the HIPAA Security Rule, which divides ePHI protection into three categories of safeguards: administrative, physical, and technical. RPM programs need each.
Technical safeguards (the five core categories):
- Access Control: unique user identification, automatic logoff, encryption and decryption. RPM platforms must enforce role-based access so a billing clerk cannot read raw vital sign data they don’t need for their job, and a care manager cannot access patients outside their assigned panel.
- Audit Controls: hardware, software, and procedural mechanisms that record and examine activity in systems containing ePHI. For RPM, this means logged audit trails of every access to a patient’s vital sign data, every device pairing event, and every export to an EHR.
- Integrity: protect ePHI from improper alteration or destruction. Critical for RPM because corrupted vital sign data can drive wrong clinical decisions. Encryption-in-transit alone doesn’t satisfy integrity. Checksums and non-repudiation are required.
- Person or Entity Authentication: verify that the person or system seeking access is who they claim. The HIPAA Security Rule has historically treated multi-factor authentication (MFA) as “addressable” rather than required. That is changing (see NPRM below).
- Transmission Security: Protect ePHI in transit. TLS 1.2 or higher is the operating standard. RPM device-to-cloud transmission should not rely on older TLS or unencrypted Bluetooth profiles.
HHS OCR HIPAA Security Rule NPRM (Notice of Proposed Rulemaking), targeted for finalization May 2026:
OCR published the NPRM on January 6, 2025 (issued December 27, 2024) proposing the most significant Security Rule update in decades. The public comment period closed in March 2025 with approximately 5,000 comments submitted. OCR’s regulatory agenda targets May 2026 for the final rule, with an effective date expected July or August 2026 (60 days after publication). Federal agencies routinely extend these deadlines, but RPM programs should plan against the proposed changes:
- MFA becomes mandatory across all systems accessing ePHI (no longer “addressable”) with limited exceptions
- Encryption at rest AND in transit becomes mandatory (no longer “addressable”) with limited exceptions
- The “required” vs “addressable” distinction is removed; all implementation specifications become required
- Vulnerability scanning at least every 6 months
- Penetration testing at least every 12 months
- 72-hour incident reporting requirement
- Patch management requirements
- Anti-malware, network segmentation, and separate backup/recovery controls for ePHI
- Compliance date: 180 days after the effective date, putting compliance in late 2026 / early 2027
- OCR’s own first-year compliance cost estimate across all covered entities and business associates: $9 billion
Business Associate Agreements (BAA) for RPM device vendors:
Every RPM device manufacturer, platform vendor, and cloud provider that handles PHI on behalf of a covered entity is a business associate under HIPAA and requires a signed BAA before any PHI flows to them. RPM programs commonly miss BAAs with smaller device manufacturers and downstream subcontractors. The BAA must address breach notification timelines (HIPAA requires within 60 days), security safeguards, subcontractor flow-down, and termination obligations.
For target keyword reference, this is the heart of HIPAA RPM compliance: technical safeguards enforced at every layer of the RPM stack, BAAs with every vendor handling ePHI, and a roadmap to meet the proposed Security Rule updates ahead of the final rule’s compliance deadline.
Device-Specific Security: BLE, Cellular, and Manufacturer Cloud Platforms
RPM device security is not generic IoT security. Each device class has its own attack surface and its own mitigation pattern.
Bluetooth Low Energy (BLE) RPM devices. Most home BP cuffs, scales, glucometers, and pulse oximeters use BLE to pair with a smartphone or hub before data reaches the cloud. The major attack vectors:
- Pairing-mode eavesdropping: devices in unsecured pairing mode can be intercepted by nearby attackers if the pairing handshake is unencrypted or uses legacy “Just Works” pairing
- Replay attacks on stored device readings if the device-to-app channel does not use sequence numbers or timestamps
- Spoofing: a malicious device impersonating a real RPM device to inject fake readings into the patient record
Mitigation: prefer devices that support BLE Secure Connections pairing (introduced in Bluetooth 4.2) and verify the device’s Bluetooth security profile during procurement. Encrypted-pairing-only mode should be enforced at the app layer, never relying on the device to default to it.
Cellular RPM devices. Some RPM hardware (especially continuous monitors and managed-service kits) uses cellular data via embedded SIM (eSIM) rather than relying on a patient’s home Wi-Fi. The cellular path bypasses the patient’s home network attacks but introduces:
- IoT cellular network security: cellular IoT typically routes through the carrier’s IoT APN. Verify whether traffic is private-APN (segregated from consumer traffic) or public-APN (shared infrastructure)
- eSIM provisioning attacks if remote SIM management is not properly authenticated
- Cellular signal jamming in dense or shielded buildings (not a confidentiality risk, but a clinical reliability risk)
Mitigation: deploy cellular RPM hardware on private APNs where the use case justifies it; require strong authentication on any remote SIM management; build clinical alert paths that detect prolonged signal loss as a care event, not just a tech issue.
Manufacturer cloud platform security. Major device manufacturers operate their own cloud platforms that ingest device data before forwarding to the RPM platform. Examples include ResMed AirView (CPAP), Philips Care Orchestrator (multiple modalities), and Dexcom Clarity (continuous glucose monitoring). Each has its own security posture, BAA terms, and integration model.
Mitigation: treat manufacturer cloud platforms as Tier 1 business associates. Require:
- Current SOC 2 Type II report or HITRUST certification
- Signed BAA with breach notification within 60 days
- Data residency commitments (US-only for ePHI in most cases)
- API authentication via OAuth 2.0 or signed JWT, not API key only
- Defined data retention and deletion policies
When a manufacturer’s cloud platform is in the data path, your RPM program’s security posture is bounded by theirs. Procurement-stage security review matters more than runtime monitoring after the fact.
For ConnectHealth-built RPM platforms, the device integration layer normalizes data from BLE, cellular, and manufacturer cloud sources into FHIR Observations with consistent encryption and audit logging, eliminating the per-device security review burden that programs face when integrating each device manufacturer separately.
Ready to Secure Your Remote Patient Monitoring (RPM) Solution?
Real-World Implementation: How We Ensured Data Security in an Elderly RPM Platform
One of our recent projects involved developing a remote patient monitoring platform tailored for elderly care. The solution combined BLE-integrated medical devices, real-time vitals tracking, and a HIPAA-compliant infrastructure to deliver both usability and data protection.
From secure Bluetooth integrations to role-based access on the web portal, we addressed every layer of security. The billing module was also built with CPT code compliance and audit-ready metrics, ensuring clinical and financial safeguards.
How PHISecure Supports HIPAA RPM Compliance on AWS
PHISecure is Mindbowser’s HIPAA compliance and PHI security platform built natively on AWS. For RPM programs running on AWS infrastructure, it provides automated compliance monitoring, encryption key management, and audit-ready reporting against the HIPAA Security Rule and Privacy Rule.
What PHISecure does:
- Automated HIPAA compliance monitoring with customizable alerts and dashboards mapped to Security Rule requirements
- Real-time risk assessment against the AWS environment hosting RPM workloads
- Audit-ready documentation that simplifies regulatory inspections, OCR audits, and customer security reviews
- AWS-native integration with Amazon S3 for encrypted PHI storage, AWS KMS for encryption key control, Amazon CloudWatch for continuous monitoring and alerting, and AWS IAM for role-based access control
- End-to-end HIPAA controls spanning data storage, encryption, access management, and breach detection
Why this matters for RPM specifically: RPM programs accumulate PHI fast. A 500-patient program ingesting daily vital sign data plus monthly management notes generates thousands of PHI records per month. Manual compliance monitoring across S3 buckets, KMS keys, IAM roles, and CloudWatch logs becomes unmaintainable above a few hundred patients. PHISecure replaces the manual review pattern with automated controls that fire on misconfigurations (an S3 bucket made public, an IAM role with excessive permissions, a missing KMS key rotation) and produce the audit trail that an OCR investigation would request.
Target buyers: healthcare providers, payers, clinics, medical practices, and digital health programs running PHI workloads on AWS. PHISecure scales from small medical practices to large health systems.
PHISecure is listed on the AWS Marketplace under Healthcare & Life Sciences professional services. Programs already on AWS can deploy PHISecure to harden their compliance posture without restructuring the underlying infrastructure.
Explore the Full Case Study: Innovating Elderly Care Through RPM
Remote Patient Monitoring and Data Security
Regular Security Audits and Updates
A proactive approach to security is essential in maintaining the integrity of remote patient monitoring (RPM) systems. Regular security audits identify vulnerabilities in systems before malicious actors can exploit them. By conducting audits, IT solution providers can assess the security posture of RPM systems and implement necessary measures to address identified risks.
Regularly updating software and firmware is crucial in patching security holes and vulnerabilities. Software updates often include patches that fix known security vulnerabilities and strengthen system defenses against potential threats. By staying updated with the latest security patches and updates, IT solution providers can mitigate the risk of security breaches and ensure the ongoing protection of patient data in RPM systems.
Common RPM Security Threats and How to Mitigate Them
Most RPM data security planning focuses on architecture and policy. The threats that actually drive incidents are operational. Here are the seven most common RPM security threat patterns and what mitigates each.
- Lost or stolen patient device with cached PHI. A patient loses the BP cuff, the cellular hub, or the bridging smartphone with stored readings. Mitigation: enforce on-device encryption with auto-wipe after 24-72 hours of inactivity, require remote-revocation capability at the app layer, and document the lost-device reporting pathway in patient education.
- Compromised care team account. Phishing or credential reuse leads to a clinical user account being compromised, exposing the RPM panel they manage. Mitigation: mandatory MFA (which the 2026 NPRM is making explicit), conditional access policies that block logins from unexpected geographies, and just-in-time elevated access rather than standing admin permissions.
- Cloud platform misconfiguration. A storage bucket is misconfigured to be publicly accessible, an IAM role is over-permissioned, or a KMS key rotation lapses. This is the number-one root cause of healthcare cloud data exposure. Mitigation: automated configuration monitoring (PHISecure on AWS handles this directly), infrastructure-as-code with security review gates, and quarterly access reviews.
- Business Associate Agreement gaps. A small device manufacturer or downstream SaaS subprocessor handles PHI without a signed BAA. When a breach happens, the covered entity carries the regulatory liability. Mitigation: maintain a current vendor inventory with BAA status, gate procurement on signed BAA before any PHI flows, and audit subcontractor flow-down annually.
- Device firmware tampering. A malicious actor with physical access to an RPM device modifies firmware to alter readings or exfiltrate data. Low-likelihood for most consumer-grade RPM hardware but high-impact when it happens. Mitigation: device manufacturer’s secure boot and signed firmware updates, plus monitoring for anomalous reading patterns at the platform layer.
- Third-party SaaS supply chain compromise. A vendor your RPM platform depends on (analytics, communications, billing) is breached, and the breach extends into your environment. The Change Healthcare incident in February 2024 (192.7 million records exposed via an Optum/UnitedHealth subsidiary, the largest healthcare data breach in world history) is the canonical example. Mitigation: minimize the number of subprocessors handling PHI, require SOC 2 Type II from each, and segment your environment so a single vendor compromise has bounded blast radius.
- Insider misuse. A clinical or operational staff member accesses patient data outside their authorized panel. Often discovered via post-incident audit log review. Mitigation: minimum-necessary access enforced at the role level, behavioral monitoring of access patterns, and quarterly access certifications by managers.
The threat distribution in healthcare is heavy on categories 2-4 and 7 (operational) rather than 1, 5, or 6 (technical or external). Investment should match.
User Education and Training
User education and training are integral in building a culture of security in remote patient monitoring. Healthcare providers and patients should be educated on best practices for data security to mitigate the risk of security incidents.
Training programs should include creating strong passwords, avoiding phishing attacks, and recognizing suspicious links or emails. By empowering healthcare providers and patients with the knowledge and skills to identify and respond to potential security threats, IT solution providers can strengthen the overall security posture of RPM systems.
By prioritizing regular security audits and updates and providing comprehensive user education and training, IT solution providers can foster a culture of security in remote patient monitoring. This proactive approach helps mitigate security risks, protect patient data, and maintain the trust and confidence of stakeholders in RPM technologies.
Safeguarding Patient Data: The Key to RPM Success
Wrapping up, it’s clear that data security is important for successful remote patient monitoring (RPM) programs. By emphasizing reliable security measures, IT solution providers can instill trust and confidence in healthcare providers and patients ensuring the safe and effective operation of RPM systems.
Data security not only safeguards sensitive patient information from unauthorized access but also bolsters the reliability and effectiveness of RPM initiatives. It’s a vital component in mitigating the risk of security incidents and enhancing the overall quality of remote patient monitoring services.
By focusing on data security in bolstering trust and guaranteeing the success of RPM programs, IT solution providers can underscore their dedication to protecting patient privacy and confidentiality. This commitment boosts patient trust in RPM technologies and strengthens the healthcare ecosystem’s capacity to deliver remote care effectively.
At Mindbowser, we understand the critical importance of maintaining data security in the development of remote patient monitoring software and solutions. Our expertise in the healthcare domain is marked by a commitment to integrating the best security measures into API and SDK-driven data systems.

Conclusion
Remote patient monitoring programs now operate in a far more demanding security and compliance environment. HIPAA Security Rule updates, FDA cybersecurity expectations, connected medical devices, and third-party vendor risks all require healthcare organizations to secure patient data across devices, cloud infrastructure, EHR integrations, and care team workflows. Encryption, role-based access controls, continuous monitoring, and vendor governance are now operational necessities for modern RPM platforms.
As RPM adoption continues to grow, healthcare providers and digital health companies must build platforms with compliance-ready infrastructure and ongoing security controls from the start. Secure device integrations, audit-ready monitoring, vulnerability management, and protected data transmission help reduce breach exposure while maintaining patient trust and regulatory readiness. Organizations that prioritize security and compliance will be better positioned to scale remote care programs safely and reliably.
Data security in RPM refers to the protocols and technologies used to protect patient information collected through remote patient monitoring systems. This includes securing data during transmission and storage, ensuring only authorized access, and maintaining regulatory compliance with HIPAA and other healthcare laws.
Remote Patient Monitoring (RPM) can be secure when proper data security measures are implemented. RPM systems utilize various technologies such as wearables, sensors, and mobile apps to collect and transmit patient data remotely. To ensure security, RPM systems should employ robust encryption techniques, strict access controls, secure storage and transmission protocols, regular security audits, software updates, and user education and training programs. Compliance with regulatory standards such as HIPAA and GDPR also contributes to the overall security of RPM.
RPM in cyber security refers to the aspect of Remote Patient Monitoring (RPM) that focuses on ensuring the security of patient data collected and transmitted by RPM systems. This includes implementing measures to protect sensitive health information from unauthorized access, data breaches, and cyber threats. RPM in cyber security involves encryption of data, access control mechanisms, secure storage and transmission protocols, regular security audits, software updates, and compliance with regulatory standards to safeguard patient privacy and maintain trust in remote monitoring technologies.
Data security in RPM systems is ensured through robust encryption techniques, strict access controls, secure storage and transmission protocols, regular security audits, software updates, and comprehensive user education and training.
HIPAA RPM compliance is the application of the HIPAA Security Rule and Privacy Rule to remote patient monitoring programs. It requires technical safeguards (access control, audit controls, integrity, authentication, transmission security), administrative safeguards (workforce training, incident response, BAA management), and physical safeguards across every layer of the RPM stack: devices, transmission paths, cloud infrastructure, and care team workflows. The 2024 OCR Notice of Proposed Rulemaking (expected to finalize in 2026) makes MFA and encryption-at-rest mandatory and adds vulnerability scanning every 6 months and penetration testing every 12 months.
RPM software that meets the FDA’s medical device definition requires premarket cybersecurity submission under Section 524B of the FD&C Act. As of the March 2026 FDA premarket guidance update, the submission must include a Security Risk Management Report, Software Bill of Materials (SBOM), detailed architecture views, penetration testing evidence, and a postmarket cybersecurity management plan. Software that qualifies for the Clinical Decision Support exemption (under 21st Century Cures Act criteria) may be out of scope, but the exemption test must be applied carefully on a per-feature basis.
Yes. Any RPM device manufacturer, platform vendor, or cloud provider that handles PHI on behalf of a covered entity is a HIPAA business associate and requires a signed BAA before PHI flows to them. The BAA must address breach notification timelines (60 days under HIPAA Breach Notification Rule), security safeguards, subcontractor flow-down obligations, and termination data return or destruction.
The Change Healthcare breach in February 2024 exposed 192.7 million individual records (Change Healthcare’s final estimate, reflected on the HHS OCR breach portal), making it the largest healthcare data breach in world history. Change Healthcare is a subsidiary of Optum (part of UnitedHealth Group). The breach reset the threat baseline for healthcare data security and accelerated regulatory action including the HIPAA Security Rule NPRM. For RPM programs, the lesson is third-party SaaS supply chain risk: minimize the number of subprocessors handling PHI, require current SOC 2 Type II reports from each, and segment your environment so a single vendor compromise has bounded blast radius.




















 BLOGS
BLOGS  NEWSROOM
NEWSROOM  CASE STUDIES
CASE STUDIES  WEBINARS
WEBINARS  PODCASTS
PODCASTS  ASSET HUB
ASSET HUB  EVENT CALENDAR
EVENT CALENDAR 






















