Discover core principles of DevSecOps, exploring how they can be effectively applied to enhance the security posture of your software while maintaining the agility needed to stay competitive in today’s fast-paced technological landscape.
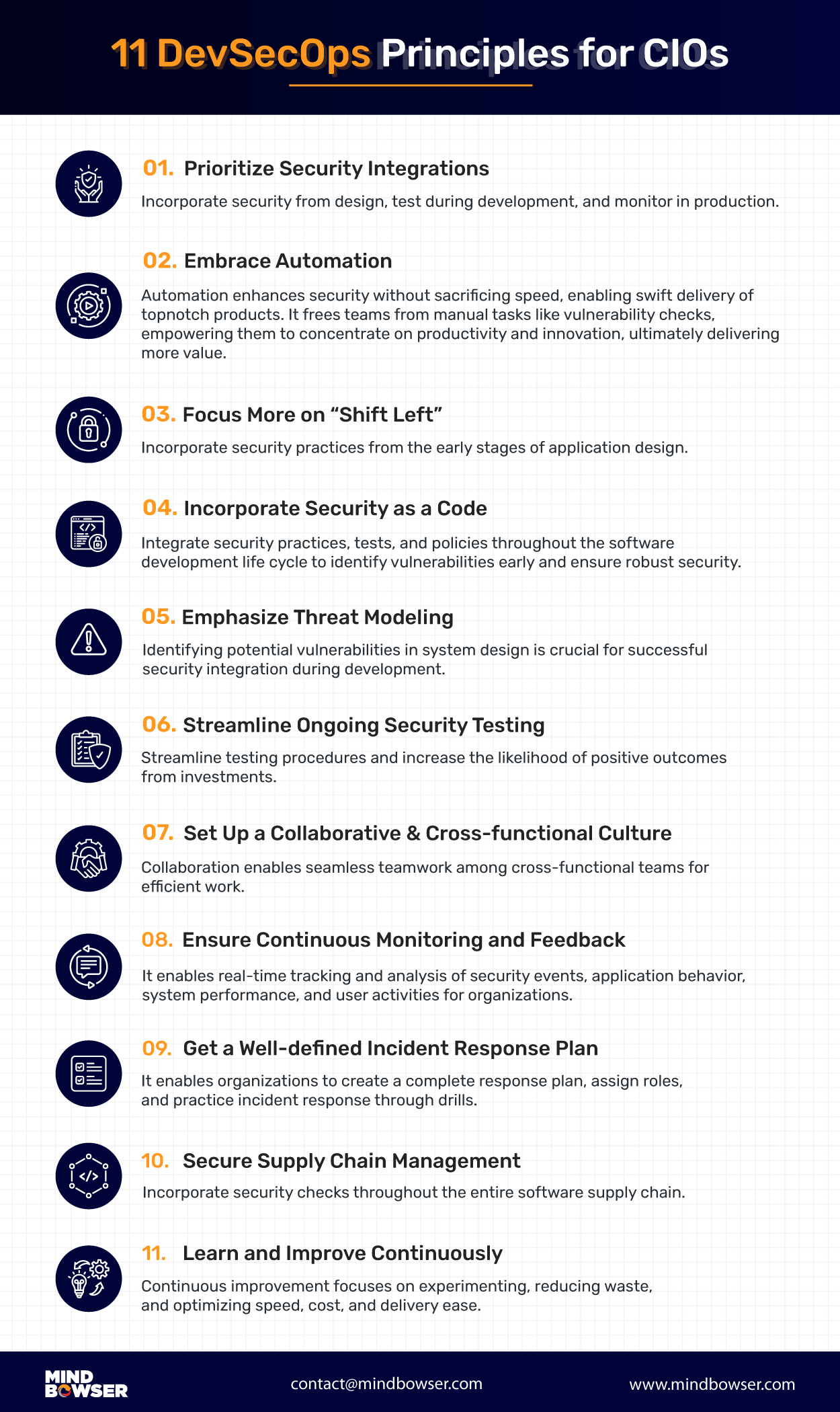
- Prioritize Security Integrations
- Embrace Automation
- Focus More on “Shift Left”
- Incorporate Security as a Code
- Emphasize Threat Modeling
- Streamline Ongoing Security Testing
- Set Up a Collaborative and Cross-functional Culture
- Ensure Continuous Monitoring and Feedback
- Get a well-defined Incident Response Plan
- Secure Supply Chain Management
- Learn and Improve Continuously
Ever increasing demand to deliver solutions or services quickly, utilizing modern development practices, highlights the importance of integrating security from the outset of the development process.
DevSecOps, as its name implies, seamlessly incorporates application security (Sec) into the development (Dev) and operations (Ops) workflows and agile processes. This approach effectively tackles urgent security concerns, making them more manageable, efficient, and cost-effective to address.
Organizations are realizing the advantages of integrating security and are planning to embrace the DevSecOps principles. Numerous surveys and reports, such as the DevSecOps Community
A survey in 2020 by DevOps.com, indicates 63% of organizations have implemented or are planning to implement DevSecOps.
As per a Gartner report in 2020, 60% of organizations by 2023 would have adopted DevSecOps principles, indicating an impressive rise from 20% in 2019. Prominent enterprises such as Capital One, Google, Verizon, and the Department of Defense (DoD) are prioritizing DevSecOps and implementing the practice in their development process.
This article delves into a range of principles that Chief Information Officers (CIOs) can employ to embrace DevSecOps within their development procedures. These principles serve to assist organizations in attaining their security objectives while simultaneously ensuring the creation of secure, resilient, and dependable products.
Furthermore, they establish mechanisms and processes that enable efficient responses to any security concerns that might arise.
Related Read: What is DevSecOps? Importance, Components, Tools, Benefits
Why Should CIOs Focus on DevSecOps Principles?
The answer lies in the significant benefits it brings to the table. By prioritizing security from the early stages of software development, CIOs are responsible for:
🔹 Developing robust security strategies
🔹 Conducting thorough risk assessments
🔹 Promoting security awareness within the organization
🔹 Collaborating closely with security teams
🔹 Evaluating secure technologies
🔹 Planning effective incident response strategies
🔹 Continuously monitoring and improving security measures.
Reasons for CIOs to Advocate for the Adoption of DevSecOps
There are numerous compelling reasons for CIOs to advocate for the adoption of DevSecOps within organizations actively:
Manage and mitigate security risks
By investing time and effort in developing a comprehensive risk management plan to identify and mitigate potential risks and threats, CIOs can help organizations to avoid significant setbacks in terms of financial resources, data assets, and reputation.
Place a compliance and regulatory framework
Developing compliance strategies, policies, and procedures ensures adherence to data protection and privacy laws ensure data protection and privacy laws adherence. By conducting audits, and fostering collaboration between the relevant stakeholders, CIOs can ensure that organizations meet their regulatory obligations while maintaining robust and secure IT operations.
Build resilient systems and applications
Fostering collaboration between cross-functional teams facilitates building resilient systems to ensure uninterrupted operations and minimize the effects of potential incidents. By regularly reviewing and analyzing data, CIOs can identify areas for improvement and drive initiatives to enhance resilience based on the lessons learned.
Optimize resource allocation
Informed decision-making helps CIOs optimize available resources by allocating them to projects and initiatives that deliver the highest business value and directly align with the organization’s strategic goals.
Incorporate speed and agility
Adopting agile development methodologies and implementing DevSecOps practices encourages rapid prototyping and experimentation techniques, leading to the implementation of CI/CD practices for frequent and automated software releases.
Agile and DevSecOps, while distinct, collaborate in their shared commitment to iterative improvements, enabling development teams to strike a balance between agility and security in the ever-evolving landscape of software development.
Deliver secure and reliable products or services:
Establishment of a comprehensive security strategy and governance framework, maintaining compliance with relevant regulations, regularly assessing the effectiveness of security measures, conducting thorough security testing and code reviews, and fostering a culture of secure coding practices help to mitigate the risk of security breaches or disruptions by ensuring the delivery of secure and reliable products or services within the organization.
11 Key DevSecOps Principles for CIOs to Adopt
Implementing DevSecOps to drive organizational transformation and reach new heights can be a daunting endeavor for CIOs. However, considering the numerous benefits associated with this approach, here are some core principles of devsecops to help you strategize the implementation of DevSecOps within your organization:
1. Prioritize Security Integrations
Historically, it was a common practice to address security concerns at the end of the development phase, which often resulted in discovering security issues toward the end of the process. Rectifying these issues incurred additional time and cost, hindering the ability to deliver functional software quickly.
To overcome these challenges, it is crucial to prioritize the early integration of security practices throughout the entire development lifecycle. This entails incorporating security considerations from the design phase, conducting security testing and code reviews during development, and implementing security monitoring and incident response capabilities in production environments.
2. Embrace Automation
Human error is the primary cause of over 95 percent of data breaches, resulting in various negative consequences. Even a minor mistake can lead to costly cybersecurity attacks.
To mitigate these risks, embracing automation in implementing DevSecOps can be highly beneficial. By utilizing self-service security tools, teams can perform pipeline vulnerability scanning, SAST (Static Application Security Testing), open-source library scanning, and more.
Automation eliminates the need to compromise security for speed, enabling the rapid delivery of high-quality products. It also eliminates manual efforts such as checking for software vulnerabilities, allowing teams to focus on productive and innovative tasks and deliver greater value.
3. Focus More on “Shift Left”
In the traditional development process, application testing, and security testing were typically conducted in the later stages resulting in delayed detection of issues, frequent back-and-forth between the security and development teams for remediation, and the probability of releasing software without adequate security measures.
By adopting a “shift security left” approach, you can implement security measures throughout the entire development lifecycle, rather than solely at the end. This approach emphasizes incorporating security practices from the early stages of application design.
By proactively identifying and addressing potential security issues and vulnerabilities early in the development process, it becomes easier, faster, and more cost-effective to mitigate security concerns.
4. Incorporate Security as a Code
The need for faster code delivery to enable frequent releases often introduces security issues. Additionally, traditional cybersecurity architectures and models are becoming outdated, exposing applications to vulnerabilities.
By adopting the security as a code (SaC) methodology, you can incorporate security practices, tests, and policies into every step of the software development life cycle. This allows developers to identify vulnerable code early on and implement security measures to address any irregularities, thereby preventing last-minute surprises during release.
Infrastructure as code (IaC) involves managing your organization’s IT infrastructure through configuration code instead of manually setting up each component. By using tools like Terraform, CloudFormation, and Ansible, you can define infrastructure configurations in code and consistently apply security controls such as firewalls, network segmentation, and encryption across environments.
5. Emphasize Threat Modeling
Traditionally, security professionals relied on whiteboard sessions to conduct threat modeling. While these meetings facilitated knowledge transfer and intelligence sharing, they proved to be time-consuming.
However, integrating threat modeling into DevSecOps workflows can help identify potential vulnerabilities in system design and architecture, making it a critical component of successful security integration in the development process. Investing in the development of a structured threat model that documents identified threats, vulnerabilities, and mitigations, is highly recommended.
Industry-standard methodologies such as:
- STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) or
- DREAD (Damage, Reproducibility, Exploitability, Affected Users, Discoverability) model can serve as a valuable guide during the threat modeling implementation process.
6. Streamline Ongoing Security Testing
In recent times, there has been a significant increase in developers releasing code faster than ever before, with over 83% acknowledging this trend. To keep pace with these rapid development methods, security considerations should not be overlooked.
To address these challenges, adopting automated testing processes can streamline your testing procedures and increase the likelihood of positive outcomes from your investments.
Various types of testing processes, such as:
- Static Analysis Security Testing (SAST)
- Dynamic Analysis Security Testing (DAST)
- Interactive Analysis Security Testing (IAST)
It can help your business streamline these processes. By leveraging these testing methodologies, you can reduce the risk of human error, detect and rectify issues earlier in the development cycle, improve response processes, and accelerate the development process, while ensuring cost-effectiveness
Helping HR Tech Company Scale: Our DevOps Implementation
7. Set Up a Collaborative and Cross-functional Culture
Breaking down silos and transforming the culture of an organization is often a challenging endeavor.
However, one of the most effective and impactful ways to address this issue is by implementing a DevSecOps culture that goes beyond simply implementing security tools and processes—it is a mindset that permeates the entire organization.
Collaboration and accountability form the foundation of this culture. Collaboration fosters seamless teamwork among cross-functional teams, enabling them to work together efficiently. Accountability ensures that each individual within the organization takes ownership and responsibility for security and reliability throughout the entire development process.
8. Ensure Continuous Monitoring and Feedback
In the ever-evolving landscape of cyber threats, relying on periodic monitoring of the IT environment can leave businesses with outdated information and expose them to undetected security risks, potentially resulting in liability or compliance fines.
To address this challenge, implementing a continuous monitoring process becomes essential. This approach allows organizations to track and analyze security events, application behavior, system performance, and user activities in real time. Continuous monitoring not only provides valuable data and insights but also enables feedback loops that empower teams to make informed decisions, identify areas for improvement, and measure the impact of their changes.
Furthermore, incorporating feedback from users and stakeholders adds valuable context and perspectives, which shape the design and implementation of effective monitoring strategies, ensuring the right metrics are captured and analyzed.
9. Get a well-defined Incident Response Plan
Even minor cybersecurity incidents, like malware infection, have the potential to escalate into significant problems that can lead to data breaches, data loss, and disruptions in business operations. In the absence of a robust incident response plan, organizations may struggle to follow proper protocols for containing and recovering from breaches once they are detected.
Implementing incident response processes allows organizations to establish a comprehensive response plan, assign roles and responsibilities, and conduct drills to practice incident response procedures. This process encompasses various steps, including detection, analysis, containment, eradication, and recovery, which collectively enable effective handling of security incidents.
By developing and implementing a well-defined incident response plan, organizations can respond to security incidents efficiently, minimize their impact, facilitate timely recovery, safeguard critical assets, and maintain the trust of customers and stakeholders.
10. Secure Supply Chain Management
The majority of software development projects involve the utilization of open-source components or third-party libraries. Unfortunately, attackers exploit the trust relationship associated with these components to introduce malware into the third-party code.
One potential solution is to incorporate security checks throughout the entire software supply chain. Adopting a DevSecOps approach for your software supply chain can help ensure its security by bringing together application developers, security professionals, and IT operations personnel (known as the DevSecOps team).
This collaborative team utilizes its collective expertise to integrate security measures at every stage of the software supply chain, which includes planning, sourcing, building (and testing), transporting, and deploying (and monitoring).
11. Learn and Improve Continuously
DevSecOps fosters a culture of continual growth and learning. Through the collection and analysis of security metrics and feedback, organizations can pinpoint areas that require enhancement and implement effective remediation strategies.
Continuous improvement is a practice that centers around experimentation, waste reduction, and optimization in terms of speed, cost, and ease of delivery. It is closely intertwined with continuous delivery, enabling DevOps teams to consistently roll out updates that enhance the efficiency of software systems.

Check How Mindbowser Have Adopted DevSecOps for Their Clients
As the momentum for embracing DevSecOps to enhance security continues to grow, it brings forth both opportunities and challenges for CIOs. The ever-evolving technological landscape further intensifies the pressure on CIOs as they strive to strike a balance between delivering secure solutions and achieving business objectives.
Mindbowser, with its profound focus and expertise in DevSecOps security practices, has been instrumental in aiding organizations to seamlessly integrate security practices into their software or solutions. Through our commitment to prioritizing and incorporating security at every stage of development, we have successfully built and delivered secure and resilient software solutions that align with your expectations and quality standards.
With a dedicated focus on enhancing DevSecOps best practices, Mindbowser leverages our extensive expertise in DevSecOps and security-focused approaches. Our profound understanding of the DevSecOps methodology empowers us to provide valuable insights and guidance on implementing effective security practices throughout the entire development pipeline. With Mindbowser’s DevSecOps services, organizations can receive valuable guidance in strategic planning by aligning their technology initiatives with business goals.
Frequently Asked Questions(FAQs)
Implementing DevSecOps in organizations involves the following key principles:
- Prioritizing Security integrations
- Shifting security left
- Automating security processes
- Emphasizing Threat modeling
- Security as code
- Continuous monitoring and feedback
- Fostering a culture of shared responsibility
CIOs can ensure security is not compromised by implementing automated security testing, integrating security controls and measures into the development pipeline, conducting regular security audits and assessments, providing security training to development teams, and establishing a strong security awareness and accountability culture
Common challenges include resistance to change, lack of security expertise, tooling and integration complexities, and balancing security with speed. CIOs can address these challenges by championing the DevSecOps initiative, providing training and resources to upskill teams, fostering cross-functional collaboration, selecting appropriate tools, and promoting a culture of continuous improvement and learning
CIOs can foster collaboration and shared responsibility by encouraging cross-functional teams, promoting open communication channels, organizing regular meetings and workshops, setting common goals and metrics for all teams, providing opportunities for joint problem-solving, and recognizing and rewarding collaborative efforts
Common tools and technologies in DevSecOps include code analysis tools, vulnerability scanners, security information, and event management (SIEM) systems, continuous integration/continuous delivery (CI/CD) platforms, and automation frameworks. CIOs should evaluate these tools based on their compatibility with existing infrastructure, ease of integration, scalability, security features, community support, and vendor reputation.
CIOs can measure the effectiveness and success of their organization’s DevSecOps practices by tracking relevant metrics that provide insights into various aspects. Some of the key metrics to consider are:
- Deployment Frequency: Measures how frequently software deployments are performed. A higher deployment frequency indicates an organization’s ability to release software updates and features more frequently and is a sign of an efficient DevSecOps process.
- Lead Time: Time taken from initiating a change to deploying it into production. Shorter lead times indicate faster delivery cycles. Tracking lead time helps assess the speed and efficiency of the development and deployment process.
- Mean Time to Recovery (MTTR): Average time taken to recover from incidents or failures. It reflects the organization’s ability to identify and resolve issues promptly, minimizing the impact on software delivery.
- Change Failure Rate: Indicates the percentage of changes or deployments that result in failures or issues. A high change failure rate may suggest potential problems in the deployment process or the need for more robust testing and quality assurance measures.