In today’s fast-paced industry staying compliant with healthcare regulations is critical and essential for success. The world of healthcare compliance provides quality patient care that meets strict regulatory requirements The developing landscape of healthcare laws and regulations can make it challenging for organizations to keep up and avoid penalty costs.
That’s why we are here to help you navigate through this complex maze with our comprehensive healthcare compliance checklist. We ensure that implementing this list can help you provide secure patient care. Let’s dive together and set your organization on a path toward successful maintenance of healthcare compliance!
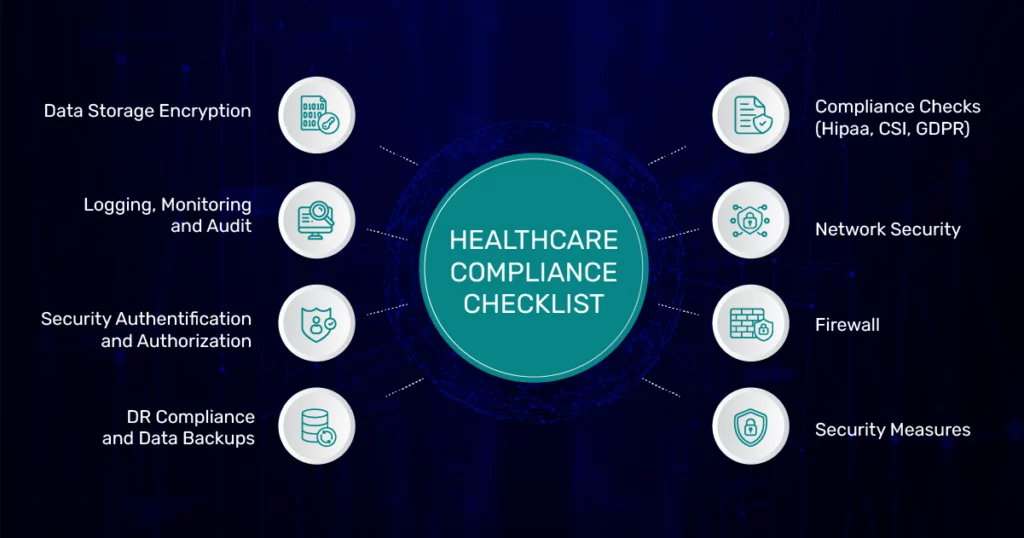
1. Data Storage Encryption
Data storage encryption is a crucial component of healthcare compliance. Encryption is the sophisticated method that transforms the data into an indecipherable format, ensuring exclusive access solely to individuals or systems with authorized credentials.
In the healthcare industry, data storage encryption is necessary to comply with various regulatory standards, such as the Health Insurance Portability and Accountability Act (HIPAA), the General Data Protection Regulation (GDPR), and the Payment Card Industry Data Security Standard (PCI DSS).
Your checklist includes encryption tasks for various data storage services like EBS, S3, RDS, and ECS. These tasks involve creating encryption keys, enabling encryption, encrypting existing files or volumes, and importing the encrypted data to the Terraform state file.
2. Logging, Monitoring & Audit
Another crucial factor in the healthcare compliance checklist is logging, monitoring, and auditing which can be achieved using a monitoring and logging stack like Open Search or Grafana, and AWS service logs like VPC, ALB, S3, RDS, and Cloudtrail.
AWS service logs and CloudTrail are essential components for monitoring and auditing activities in the AWS environment for the healthcare industry.
🔸 AWS Service Logs
We all know AWS (Amazon Web Service) offers a wide range of cloud computing services that helps businesses scale and manage their applications and infrastructure. One of the essential aspects of operating the cloud is monitoring and analyzing the activities and events within your AWS environment. AWS provides different logging services that capture valuable information about the behavior and performance of your AWS resources.
AWS service logs play a crucial role in evaluating the performance of your cloud infrastructure. They are generated by different AWS services like Amazon S3, Amazon EC2, AWS Lambda, and many others with detailed records of events, errors, and other relevant information. We have listed some of the AWS service logs that can help you with healthcare compliance;
🔹 VPC Flow Logs: Enabling VPC flow logs allows you to capture information about the IP traffic going to and from network interfaces in your VPC. This can help you troubleshoot connectivity issues, detect and respond to security incidents, and comply with regulatory requirements.
🔹 ALB Logs: Configuring logs for Application Load Balancers (ALBs) enables you to capture information about the incoming traffic to your web applications. This can help you diagnose issues, troubleshoot errors, and monitor the performance of your applications.
🔹 S3 Access Logs Configuration: Configuring access logs for Amazon S3 buckets allows you to track the requests made to your buckets and analyze the usage patterns. This can help you identify anomalies, detect unauthorized access, and optimize your storage usage.
🔹 Server Access Logs: Configuring server access logs for EC2 instances enables you to record information about the incoming requests and responses to your applications. This can help you diagnose issues, monitor performance, and comply with regulatory requirements.
Related Read: Building HIPAA-Compliant Software Using AWS Cloud
🔸 CloudTrail
CloudTrail is another AWS service that enables you to monitor and record the activity within AWS. The detailed logs offer a comprehensive view of actions taken within the environment. Compliance regulations such as HIPAA, require organizations to implement controls and measures to ensure the security and privacy of healthcare data.
CloudTrail helps meet these requirements by providing audits to track and investigate any unauthorized or suspicious activities within your AWS environment. With CloudTrail, you can easily maintain the integrity and confidentiality of sensitive healthcare information.
🔹 Creating a Trail with CloudTrail: CloudTrail is a service that provides the event history of your AWS account activity, including actions taken through the AWS Management Console, AWS SDKs, command-line tools, and other AWS services. Creating a trail with CloudTrail allows you to log, monitor, and retain events for compliance and security purposes.
🔹 CloudWatch Log Group: CloudWatch is a service that provides monitoring and logging capabilities for AWS resources and applications. Creating a CloudWatch log group enables you to store and analyze the CloudTrail logs in a centralized location.
🔹 Creating an SNS Topic: SNS is a service that provides messaging and notification capabilities for AWS resources and applications. Creating an SNS topic allows you to receive alerts and notifications when CloudTrail events occur.
Create an Alarm: Creating an alarm in CloudWatch allows you to monitor the CloudTrail logs for specific events and trigger actions based on predefined thresholds or conditions. This can help you automate responses to security incidents, compliance violations, or performance issues.
3. Security Authentication and Authorization
Now Security authentication and authorization are the key aspects to consider while managing sensitive data within any system. Authentication ensures that only authorized users or entities are granted access to protect sensitive information.
Adding authentication and authorization measures in the compliance checklist ensures authorized access to the information and defines what actions an authenticated entity can perform in the application.
🔸 S3 + CF Assets Security Using Pre-signed and Signed URLs
When it comes to securing assets in AWS and CloudFront, pre-signed URLs and signed URLs are two important mechanisms that can be used. It includes authentication information, allowing recipients of the URL to access specific data for a limited period of time.
Signed URLs are often used for temporary access to specified CloudFront content, without exposing the CloudFront distribution or using predefined URLs for S3 objects directly. With signed URLs, you get access to features like limited access to specified IP addresses or restricted access to a specified time frame.
🔹 Creating Key Groups: In AWS CloudFront, you can use private content in your distributions. A key group contains the public keys to verify the signature on signed URLs.
🔹 Updating CloudFront Template for Origin Restriction and Signature Request: Updating the CloudFront Template for Origin Restriction and Signature Request enables you to restrict access to your S3 content and protect it from unauthorized access. You can specify the allowed origin domains and the signature requirements for accessing the content.
🔹 Testing: Testing the setup for pre-signed and signed URLs is necessary to ensure that the configuration works as intended and provides security.
🔸 IAM Best Practices
IAM (Identity and Access Management) best practices refer to a set of guidelines for effectively managing user identities and access to resources within an organization‘s AWS environment. The IAM best practices focus on establishing and implementing security measures to protect sensitive healthcare data, prevent unauthorized access, and maintain compliance with industry regulations.
🔹 MFA: Enabling Multi-Factor Authentication (MFA) for IAM users adds a layer of security to the AWS environment by requiring users to provide a second authentication factor, such as a code generated by a smartphone app or a hardware token.
🔹 Least Access to Policies: Providing the Least Access to Policies is a best practice for IAM that limits the permissions granted to IAM users and roles to only what is necessary to perform their job functions.
🔹 Key Rotation: Key Rotation is a best practice for IAM that involves regularly rotating access keys and secret keys for users to reduce the risk of unauthorized access to the AWS environment.
🔸 Authentication Using External Identity Pools
Businesses can integrate external identity providers (IdPs) with AWS Cognito, a fully managed service for user authentication and authorization. It allows users to authenticate with their existing credentials from external sources like social media platforms, directories, or custom identity systems.
By including “authentication using external identity pools” in a healthcare compliance checklist, organizations can ensure that user authentication processes are secure, user-friendly, and compliant with industry standards.
Optional: Authentication using External Identity Pools allows you to use external identity providers, such as social media platforms, to authenticate users and grant them access to your AWS resources. This can be a useful option for healthcare organizations that must provide access to their systems to external partners or customers.
4. DR Compliance and Data Backups
In the realm of disaster recovery (DR) compliance and data backups, the primary objective is to establish measures that guarantee business continuity and enable seamless data recovery in the event of a disaster or outage. The critical aspects focus on protecting business operations and mitigating potential disruptions caused by unforeseen events.
🔸 EC2 Backup Policies
Creating backup policies for EC2 instances is important to ensure that your critical data is backed up regularly to protect against data loss in case of any disaster or outage.
🔸 RDS Backup Policy and Multi-AZ Setup
RDS (Relational Database Service) is a managed database service provider by AWS that helps healthcare providers simplify the setup, operation, and scale of relational databases in the cloud. The backup policy includes setting up a backup, which is a periodic snapshot of the database. It determines the frequency and retention of periods of these backups.
On the other hand, Multi-AZ setup or deployment is a high-availability feature provided by AWS RDS. The AWS automatically replicates your primary database to a standby instance in a different availability zone. We are going to apply the RDS backup policy and Multi-AZ setup to achieve compliance in our healthcare product.
🔹 RDS Backup Policy: Setting up a backup policy for your RDS instances allows you to create automated backups and snapshots of your data, which can be used to restore your database in the event of an outage or data loss.
🔹 Multi-AZ Setup: Multi-AZ setup is a feature of RDS that allows you to create a standby replica of your database in a different availability zone. This provides high availability and automatic failover in the event of a disaster or outage.
🔸 S3 Versioning, Archival, and Cross-Region Replication
🔹 Versioning: Enabling versioning for your S3 buckets allows you to preserve, retrieve, and restore every version of an object in the bucket, which can be useful in the event of accidental deletion or modification of data.
🔹 Archival: Archiving data in S3 Glacier or S3 Glacier Deep Archive can be a cost-effective way to store infrequently accessed data for long-term retention.
🔹 Cross-Region Replication: Enabling cross-region replication for your S3 buckets allows you to replicate objects across different regions, which can help you meet compliance requirements and provide high availability and durability for your data.
Ensure that Your Healthcare System or Product Adheres to Compliance Standards
5. Compliance Checks (HIPAA, CSI, GDPR)
Compliance checks ensure that any software or system used in the healthcare industry meets the regulatory requirements of HIPAA, CSI, and GDPR. Once the regulatory requirements are understood the organization can perform an analysis of the compliance gap. The analysis can help you evaluate the current software or system against the requirements specified by the regulations. We have listed down three methods through which you can achieve compliance and run check-in your healthcare product;
1. Deploy the Compliance Tool and Generate Reports
Deploying compliance tools and generating reports are crucial practices for healthcare organizations to ensure and determine compliance with different regulatory requirements. We have listed down some tools that can help you deploy compliance and generate reports for your healthcare organization.
🔹 Prowler Deployment: Prowler is an open-source tool that automates compliance testing for AWS environments. Deploying Prowler allows you to run automated tests on your AWS environment and identify security issues or compliance violations.
🔹 Automated Reports Generation: Automating the report generation process for Prowler or any other compliance tool allows you to quickly and easily generate compliance reports for your AWS environment.
2. AWS Trust Advisor
AWS Trust Advisor is a free service that provides recommendations to help you optimize your AWS infrastructure for security, cost, performance, and fault tolerance.
3. Tests and Audit
🔹 AWS Well-Architected Scan: Conducting an AWS Well-Architected Scan allows you to review and improve your AWS architecture based on best practices and compliance requirements. The scan covers five pillars of AWS Well-Architected Framework: operational excellence, security, reliability, performance efficiency, and cost optimization.
6. Network Security
Network security is another critical aspect of healthcare compliance and plays an important role in securing sensitive patient data, and maintaining the integrity and confidentiality of healthcare systems. Healthcare organizations can implement VPC security to configure security in cloud environments such as AWS. VPC allows organizations to define and control isolated sections of the cloud where they can deploy different resources like virtual servers, databases, and storage.
🔸 VPC Security
🔹 S3 Endpoints: S3 endpoints are virtual devices that allow you to connect to S3 buckets securely without going through the public internet. Creating S3 endpoints for your VPC can improve security by reducing the attack surface.
🔹 Custom NACL Rules: Network Access Control Lists (NACLs) allow you to control inbound and outbound traffic at the subnet level. Creating custom NACL rules can help you implement more granular control over your network traffic.
🔹 Security Groups: Security groups act as a virtual firewall that controls inbound and outbound traffic to instances in a VPC. Implementing appropriate security groups is essential to ensure that only authorized traffic can access your instances.
🔸 WAF
A web Application Firewall is a security solution designed to secure web applications from various types of cyber attacks. A WAF operates under the application layer of the network stack, which examines and filters HTTP/HTTPS traffic within an application and its users.
🔹 Creating a WAF: A Web Application Firewall (WAF) helps protect your web applications from common web exploits that could affect application availability, compromise security, or consume excessive resources.
🔹 Applying to Resources: Once you have created a WAF, you must apply it to the appropriate resources to protect them from potential security threats.
7. Firewall
You can ensure network security in your healthcare organization with the help of a Firewall. A Firewall acts as a barrier between an organization’s internal and external networks, evaluating and controlling incoming and outgoing traffic based on predetermined rules. The Firewall is the first line of protection that secures the network perimeter. Healthcare providers and organizations can inspect traffic from various sources, reducing the risk of data breaches and unauthorized access.
🔸 AWS Inspector
AWS Inspector is an automated security assessment service that helps you identify vulnerabilities and security issues in your EC2 instances and applications. It is a cost-effective way to maintain the security of your AWS environment and ensure that it complies with industry standards. The cost of AWS Inspector is 1.2528$ per instance/per month after the 15-day free trial.
🔸 AWS Guard Duty
It is a threat detection service that helps you identify potential security threats in your AWS environment, including unauthorized access, compromised instances, and malicious activity. AWS Guard Duty costs $3.00 per 1,000 CloudTrail events analyzed, up to $100 per month after the 30-day free trial.
🔸 AWS Security Hub
We provide a comprehensive view of your security posture across your AWS accounts and help you identify security threats and vulnerabilities. AWS Security Hub is included with AWS accounts at no additional charge. However, you may incur additional costs for using other AWS services integrated with Security Hub, such as AWS Inspector and AWS Guard Duty.
8. Security Measures
It is important to implement appropriate security measures to protect sensitive healthcare data. Our development team carries out a few measures when it comes to security and compliance.
🔸 Short-lived Access Tokens
Short-lived access tokens expire after a certain amount (not more than 15 minutes). This is an important security measure to prevent unauthorized access to sensitive healthcare data.
🔸 Handling Session Timeouts
Session timeouts are an important security measure to prevent unauthorized access to sensitive healthcare data. We implement automatic logouts and listeners during session timeouts to invalidate the tokens is a good practice.
🔸 Tokenization for PII or Sensitive Data
Tokenization is a method of protecting sensitive healthcare data by replacing it with a non-sensitive token. By leveraging tokenization, we help prevent unauthorized access to sensitive data.
🔸 User Authentication with Database Using Salt Value Along with the Password for Hashing
Using a salt value along with the password for hashing can help prevent unauthorized access to user data.
🔸 Storing the Token in UI Only in Temporary Storage or Variable and Not in Local Storage
We prevent unauthorized access to sensitive healthcare data. Storing the token in UI only in temporary storage or variable and not in local storage can help prevent unauthorized access to the token.
🔸 PKCE Flow for OAuth2
Implementing the PKCE flow for OAuth2 at the UI end is a good practice for securely handling authentication and authorization.
🔸 BCrypt Algorithm for Password Encoding
The team implements the BCrypt algorithm for password encoding, which is a good practice for securely storing user authentication data. Authorization should happen only if authentication is successful and the token is valid.
🔸 Sensitive and PII Data Masking in the Logs
Masking sensitive and PII data in the logs is a good practice for protecting sensitive healthcare data.
🔸 S3 + CF Assets Security Using Pre-signed and Signed URLs
Using pre-signed and signed URLs is a good practice for securely accessing S3 and CloudFront assets. This helps to prevent unauthorized access to sensitive healthcare data.

Start Ensuring Compliance Today with Our Healthcare Checklist
Developing software or a system for the healthcare industry requires compliance with various regulations and guidelines to ensure the confidentiality, integrity, and availability of patient data. This healthcare compliance checklist includes various components such as data storage encryption, network security, backup and disaster recovery, compliance checks, and user authentication and authorization.
Implementing these components ensures the system is secure, reliable, and compliant with relevant regulations such as HIPAA, CSI, and GDPR. Development teams need to follow best practices and implement security measures such as short-lived access tokens, handling session timeouts, tokenization of sensitive data, and user authentication with a salt value for hashing. By adhering to this healthcare compliance checklist, development teams can build a secure and reliable system that meets the needs of the healthcare industry.
The three main areas of healthcare compliance are:
- Patient Safety: This is the top priority and focuses on preventing medical errors, ensuring proper infection control, and safeguarding patients throughout their care journey.
- Patient Privacy and Data Security: This area ensures patient information is protected. It involves following regulations like HIPAA to keep sensitive health data secure and prevent unauthorized access.
- Billing and Coding Compliance: This ensures accurate and ethical billing practices. Healthcare providers need to follow specific guidelines to prevent fraud and ensure they are reimbursed correctly for services rendered.
A compliance checklist is a detailed document that helps organizations systematically track and verify their adherence to regulations, standards, or internal policies. It acts as a roadmap, outlining specific requirements that need to be met to ensure compliance.
Building a compliance checklist involves pinpointing the regulations you must follow, then translating those rules into actionable steps for your organization. Assign clear ownership for each task and determine how you’ll document your compliance efforts. Regularly review and update the checklist to reflect any changes in regulations and ensure it stays relevant to your evolving needs.
A compliance audit tool is a software program that helps streamline the process of conducting compliance audits. These tools can automate tasks like data collection, risk assessment, and reporting, making audits more efficient and less error-prone. Some tools even offer features to manage ongoing compliance efforts, like document management and training assignment.