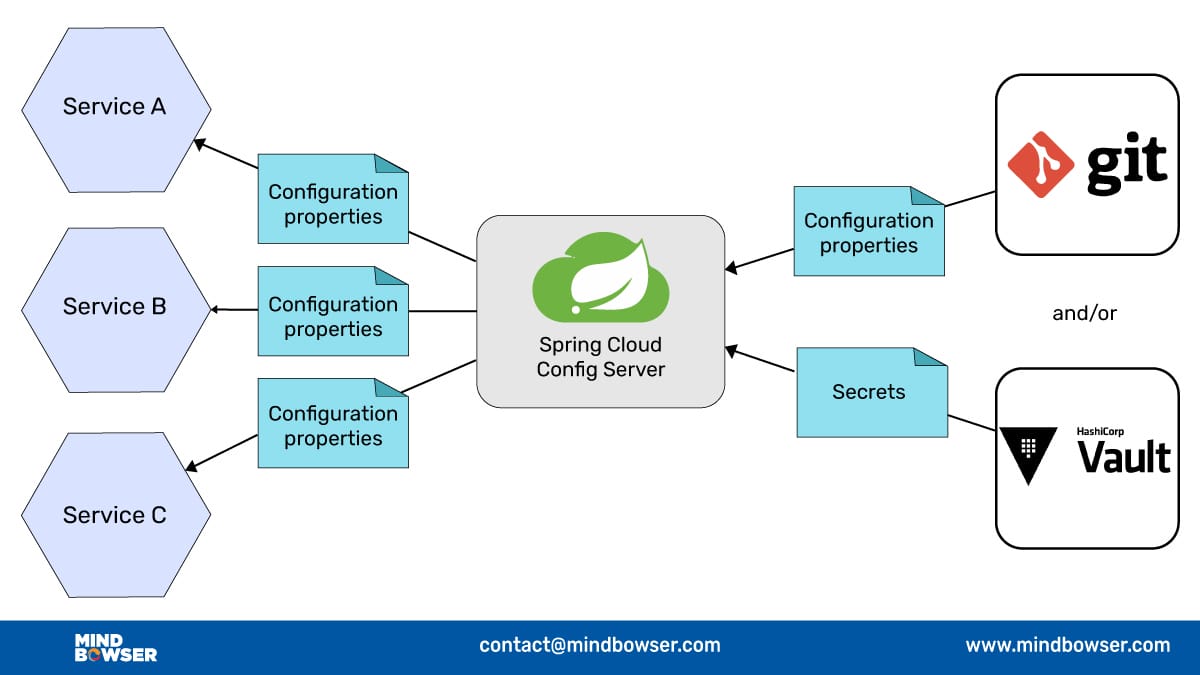
Spring Cloud Config is a way to manage settings for your applications, like database URLs, API keys, feature flags, and other parameters, in a separate and dedicated place.
This separate place, known as the “configuration server,” holds all these settings, and your applications can fetch their configurations from there.
Related read: Secure Microservices Configuration Using Spring Cloud Config
Before Spring Cloud Config
Before the introduction of Spring Cloud Config, managing configurations in a microservices architecture posed significant challenges. In the dynamic landscape of software development, particularly in the realm of microservices, individual services often have their own configuration files containing critical information such as database details, API keys, and various parameters. As the number of microservices grew within a system, maintaining and updating these configurations became a cumbersome task.
Changes required manual updates, and ensuring consistency across services, especially in different environments, proved to be a daunting challenge. This complexity hindered the scalability, security, and efficiency of configuration management. The introduction of Spring Cloud Config addressed these pain points by providing a centralized solution, streamlining the management of configurations, and enhancing the overall agility and reliability of microservices-based applications.
Related read: Microservice Architecture Using Eureka Server
Use Case
A Microservices-Based E-commerce Platform
Imagine you’re part of a development team building an e-commerce platform. Your platform is composed of various microservices, such as a product catalog, shopping cart, user authentication, and order processing. Each of these microservices has its own set of configuration parameters, including database connection details, API keys, logging levels, and more. Managing these configurations across a growing number of microservices can quickly become unwieldy.
Here’s where Spring Cloud Config becomes invaluable.
Introduction
In today’s dynamic software development landscape, microservices have emerged as a powerful architectural pattern. They offer numerous benefits, including scalability, flexibility, and faster development cycles. However, managing the configuration of multiple microservices can quickly become a daunting task. This is where Spring Cloud Config comes to the rescue, providing a centralized solution for configuration management. In this tech blog, we’ll explore a descriptive use case of Spring Cloud Config in a real-world scenario.
Problem Statement
As the e-commerce platform evolves, it’s becoming increasingly difficult to manage the configuration of each microservice separately. Changes require manual updates, and ensuring consistency and security across services is a challenge. Furthermore, rolling out configuration changes and maintaining different configurations for development, staging, and production environments is time-consuming.
Solution:
Spring Cloud Config provides a solution for the aforementioned challenges. Let’s break down the use case step by step:
1. Centralized Configuration Repository:
🔶 With Spring Cloud Config, you set up a centralized configuration repository, typically using Git. This Git repository will hold all the configuration files for your microservices.
🔶 The configuration files are structured based on application names, environments (e.g., dev, staging, prod), and profiles (e.g., default, production).
2. Configuration Server:
🔶 Create a Spring Cloud Config Server, which acts as the configuration server for your microservices. This server pulls configuration data from the Git repository.
🔶 The server provides a RESTful API that microservices can use to fetch their configurations.
3. Microservices Integration:
🔶 Each microservice integrates with the Spring Cloud Config Server by specifying its application name, environment, and profile in its `bootstrap.properties` or `bootstrap.yml` file.
🔶 When a microservice starts, it contacts the Config Server to fetch its configuration. This configuration can be automatically refreshed without requiring the microservice to restart.
4. Securing Configurations:
🔶 Spring Cloud Config provides options for securing sensitive information within your configuration files using encryption and decryption mechanisms, ensuring that your data is safe.
5. Dynamic Updates:
🔶 Changes to the configuration in the Git repository are immediately available to all microservices, simplifying the process of rolling out updates.
🔶 You can also trigger configuration refresh manually, allowing for dynamic updates without requiring a full application restart.
6. Profile and Environment-Specific Configurations:
🔶 Spring Cloud Config allows you to manage different configurations for various profiles and environments. For instance, you can have separate configurations for development, testing, and production environments.
Benefits:
🔸 Consistency: All microservices have access to consistent configurations.
🔸 Security: Sensitive data can be encrypted and securely managed.
🔸 Scalability: As the number of microservices grows, Spring Cloud Config ensures that configuration management remains efficient and straightforward.
🔸 Versioning: With a Git-backed repository, you have version control and a history of your configurations.
✔️ Spring Cloud Config can be Configured in 3 Ways:
🔸 Through git
🔸 From database
🔸 From file-based storage
In this article, I will not show you how to set up spring cloud config as it is available on the internet easily.
Today I’ll show you the most common ways developers use to safeguard their properties file.
As we all know, property files can store sensitive information about our application, so it is our job to safeguard that information.
Check out What it Takes to Build a Successful App Here
The two ways we are going to see are ➡️
1. Encryption and Decryption
2. Using .ssh key
Encryption and Decryption :
One way to secure property files is by encrypting sensitive values and decrypting them at runtime. By doing so, even if an attacker gains access to the properties files, they won’t be able to read the sensitive information without the decryption key.
To Enable Encryption and Decryption in Spring Cloud Config, Follow These Steps:
Java Cryptography Extension (JCE):
Ensure that you have the Java Cryptography Extension installed, especially if you are using Java 8 or below.
Configuration on the Config Server:
Open the application.properties file of your Config Server.
Add the following property: encrypt.key=<encryption_key>, where <encryption_key> is a secure passphrase or key that will be used for encryption and decryption.
Encrypting Sensitive Properties:
Identify the properties in your configuration files that contain sensitive information.
Prefix the sensitive properties with {cipher} to indicate that they need to be encrypted.
For example my.password={cipher}ABC12345
Encryption Process:
Use the Spring Cloud Config client or API to send a POST request to the Config Server’s /encrypt endpoint, passing the sensitive property value as the request body.
The Config Server will encrypt the value using the configured encryption key and return the encrypted result.
Replace the original value in the properties file with the encrypted value.
Decrypting Properties at Runtime:
When the client microservice requests configuration from the Config Server, the encrypted properties will be fetched.
The client microservice should have the same encryption key configured in its application.properties file.
Spring Cloud Config will automatically decrypt the properties with the matching encryption key, making them available for use.
Using .ssh key :
Another approach to secure the communication between the Config Server and the client microservices is by utilizing SSH keys. This method ensures secure authentication and data transfer.
To Use SSH Keys With Spring Cloud Config, Follow These Steps:
Generate SSH Key Pair:
Generate an SSH key pair using tools like ssh-keygen.
The key pair consists of a private key (kept secret on the client side) and a public key (added to the authorized keys on the Config Server).
Configuration on the Config Server:
Store the public key generated in the previous step on the Config Server. This can be done by adding it to the .ssh/authorized_keys file.
Configuration on the Client Microservices:
Configure the client microservices to use the corresponding private key for authentication with the Config Server.
This can be done by setting the spring.cloud.config.server.ssh.private-key property in the client’s application.properties file.
spring.cloud.config.server.git.private-key= \
-----BEGIN RSA PRIVATE KEY-----\n\ xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx\n\ xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx\n\ xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx\n\ xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx\n\ xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx\n\ -----END RSA PRIVATE KEY-----\n
Note: remember to add \n\ after every line end

Conclusion:
In this article, we explored two common methods for safeguarding properties files in Spring Cloud Config: encryption and decryption, and the use of SSH keys. These techniques provide an extra layer of security for managing sensitive configuration data in a distributed system. By implementing these measures, developers can ensure the confidentiality and integrity of their application’s property files.
We’ve also seen how Spring Cloud Config solves the challenge of managing configurations for a complex microservices-based e-commerce platform. It offers centralized, secure, and scalable configuration management, making it an essential tool for any organization embracing microservices architecture.
By adopting Spring Cloud Config, your development team can achieve greater efficiency, maintain consistency, and respond to changing requirements with ease, ultimately enhancing the agility and reliability of your microservices ecosystem.




















 BLOGS
BLOGS  NEWSROOM
NEWSROOM  CASE STUDIES
CASE STUDIES  WEBINARS
WEBINARS  PODCASTS
PODCASTS  ASSET HUB
ASSET HUB  EVENT CALENDAR
EVENT CALENDAR