JWT, Opaque Tokens, RBAC & Production-Ready Security
Modern backend systems rarely depend on a single identity provider. A real-world Spring Boot application often needs to accept tokens issued by Auth0, Azure Active Directory, Google, Okta, or even internal identity platforms — while enforcing consistent role-based access control (RBAC) across all users.
In this article, we’ll design a clean, extensible authentication architecture using Spring Security that supports:
- Multiple identity providers simultaneously
- JWT and opaque token formats
- Centralized authorization logic
- Spring Security 6+ and OAuth 2.1 best practices
This approach scales from SaaS products to enterprise platforms without locking your application into a single IdP strategy.
Why Multi-Provider Authentication Is a Real Requirement
Different users authenticate in different ways:
- SaaS customers → Auth0
- Enterprise employees → Azure AD
- Public or education users → Google
- Partners & integrations → Okta
Yet your backend must:
- Trust tokens from multiple issuers
- Validate provider-specific claims
- Enforce the same authorization rules
Spring Security provides the primitives — but real systems need a layer above the defaults.
Token Diversity: JWTs, Opaque Tokens & Trust Boundaries
Not all access tokens behave the same:
| Token Type | Characteristics |
| JWT | Self-contained, signed, locally validated |
| Opaque | Reference tokens validated via introspection |
| Custom | Provider-specific formats and claims |
Each identity provider represents a separate trust boundary:
- Different signing keys
- Different claim semantics
- Different failure modes
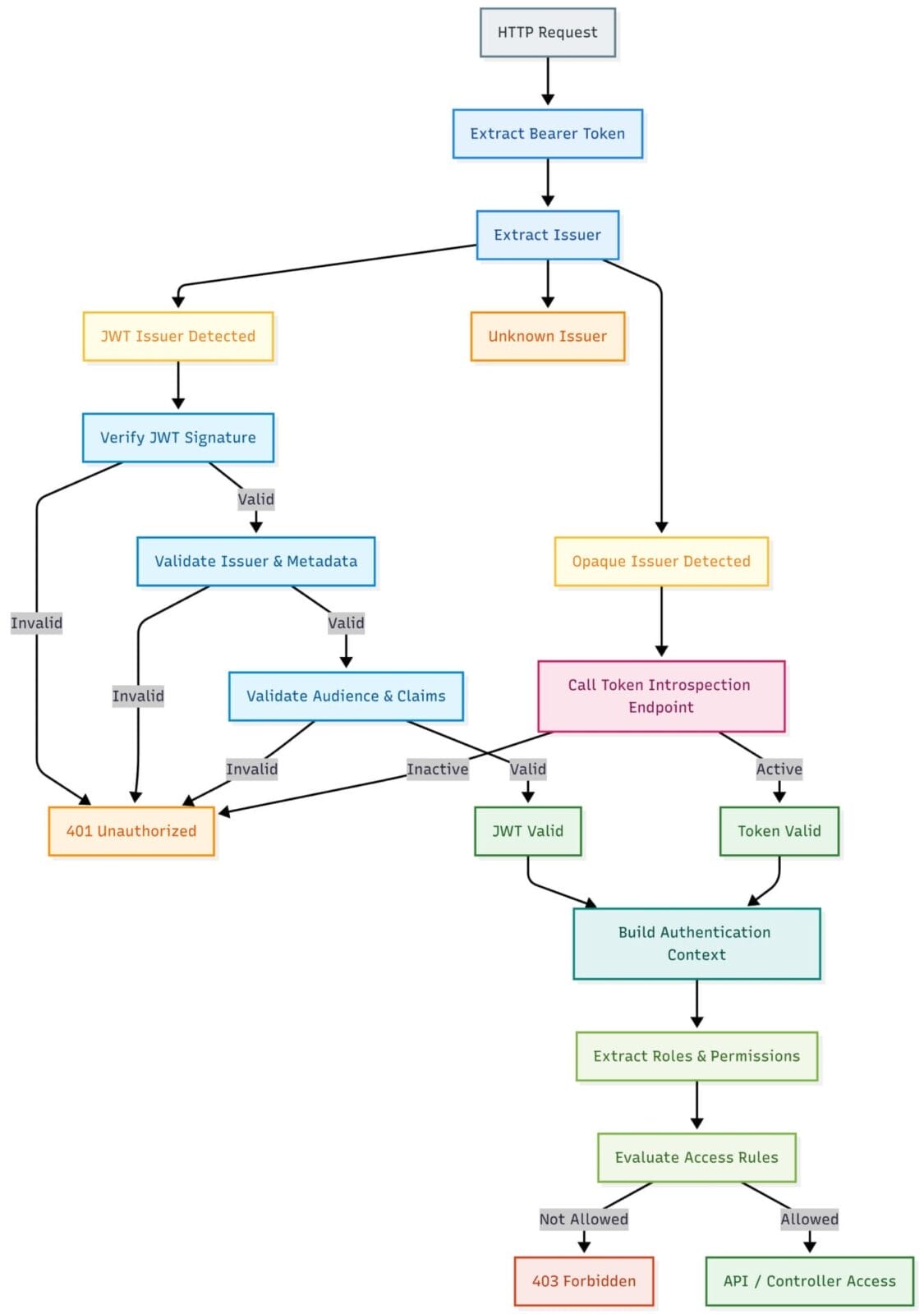
Core Design: Runtime Authentication Resolution
Rather than hard-coding providers in configuration, we dynamically resolve how a token should be validated at runtime based on its issuer.
Benefits
- No provider logic in controllers
- One unified security entry point
- Easy onboarding of new identity providers
- Clear separation of responsibility
Issuer-Based Authentication Manager Resolver
@Component
@RequiredArgsConstructor
public class IssuerAuthManagerResolver
implements AuthenticationManagerResolver<HttpServletRequest> {
private final TokenIssuerExtractor issuerExtractor;
private final TokenValidatorRegistry validatorRegistry;
@Override
public AuthenticationManager resolve(HttpServletRequest request) {
return authentication -> {
BearerTokenAuthenticationToken bearer =
(BearerTokenAuthenticationToken) authentication;
String token = bearer.getToken();
String issuer = issuerExtractor.extract(token);
TokenValidator validator =
validatorRegistry.findByIssuer(issuer);
return validator.authenticate(token);
};
}
}This keeps Spring Security configuration clean and provider-agnostic.
Spring Security Configuration (Spring Security 6+)
Dependencies
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-security</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-oauth2-resource-server</artifactId>
</dependency>Security Filter Chain
@Bean
SecurityFilterChain securityFilterChain(HttpSecurity http) throws Exception {
http
.csrf(AbstractHttpConfigurer::disable)
.authorizeHttpRequests(auth ->
auth.anyRequest().authenticated()
)
.oauth2ResourceServer(oauth ->
oauth.authenticationManagerResolver(authManagerResolver)
);
return http.build();
}Stateless
No deprecated APIs
Compatible with Spring Boot 3.x & Jakarta EE
Need guidance on JWT, OAuth2, or RBAC implementation? Talk to an expert today.
Token Validator Registry
Instead of conditional logic scattered across the codebase, we centralize provider resolution.
@Component
@RequiredArgsConstructor
public class TokenValidatorRegistry {
private final Auth0JwtValidator auth0Validator;
private final AzureAdJwtValidator azureValidator;
private final GoogleJwtValidator googleValidator;
private final OktaOpaqueTokenValidator oktaValidator;
public TokenValidator findByIssuer(String issuer) {
if (issuer.contains("auth0.com")) return auth0Validator;
if (issuer.contains("login.microsoftonline.com")) return azureValidator;
if (issuer.contains("accounts.google.com")) return googleValidator;
if (issuer.contains("okta.com")) return oktaValidator;
throw new SecurityException("Unsupported issuer: " + issuer);
}
}Adding a new provider requires only a new validator, not a redesign.
JWT Validation Example (Auth0)
@Component
@RequiredArgsConstructor
public class Auth0JwtValidator implements TokenValidator {
private final AuthenticationFactory authenticationFactory;
private final AudiencePolicy audiencePolicy;
@Override
public Authentication authenticate(String token) {
NimbusJwtDecoder decoder =
JwtDecoders.fromIssuerLocation("https://auth0-domain/");
decoder.setJwtValidator(
new DelegatingOAuth2TokenValidator<>(
JwtValidators.createDefault(),
new AudienceValidator(audiencePolicy.allowedAudiences())
)
);
Jwt jwt = decoder.decode(token);
return authenticationFactory.fromJwt(jwt, Provider.AUTH0);
}
}Opaque Token Validation Example (Okta)
@Component
@RequiredArgsConstructor
public class OktaOpaqueTokenValidator implements TokenValidator {
private final AuthenticationFactory authenticationFactory;
@Override
public Authentication authenticate(String token) {
SpringOpaqueTokenIntrospector introspector =
new SpringOpaqueTokenIntrospector(
"https://{okta-domain}/oauth2/v1/introspect",
"client-id",
"client-secret"
);
OAuth2AuthenticatedPrincipal principal =
introspector.introspect(token);
return authenticationFactory.fromOpaque(principal, Provider.OKTA);
}
}Custom Claim & Tenant Validation
@Component
public class AudienceValidator implements OAuth2TokenValidator<Jwt> {
private final Set<String> allowedAudiences;
public AudienceValidator(Set<String> allowedAudiences) {
this.allowedAudiences = allowedAudiences;
}
@Override
public OAuth2TokenValidatorResult validate(Jwt jwt) {
boolean valid =
jwt.getAudience().stream()
.anyMatch(allowedAudiences::contains);
if (!valid) {
return OAuth2TokenValidatorResult.failure(
new OAuth2Error("invalid_audience")
);
}
return OAuth2TokenValidatorResult.success();
}
}This design easily extends to:
- Multi-tenant validation
- Subscription tiers
- Organization boundaries
Unified Authentication Context & RBAC
@Component
public class AuthenticationFactory {
public Authentication fromJwt(Jwt jwt, Provider provider) {
Set<GrantedAuthority> authorities =
jwt.getClaimAsStringList("permissions")
.stream()
.map(SimpleGrantedAuthority::new)
.collect(Collectors.toSet());
DefaultOAuth2AuthenticatedPrincipal principal =
new DefaultOAuth2AuthenticatedPrincipal(
jwt.getClaims(),
authorities
);
return new BearerTokenAuthentication(
principal,
new OAuth2AccessToken(
OAuth2AccessToken.TokenType.BEARER,
jwt.getTokenValue(),
null,null
),
authorities
);
}
}Centralized RBAC
Provider-agnostic authorization
Ready for ABAC evolution
Handling Failure Modes Explicitly
Authentication systems fail in predictable ways:
- Token introspection endpoints become unavailable
- Issuer metadata rotates
- Claims change unexpectedly
This architecture limits blast radius by:
- Isolating failures per provider
- Avoiding global authentication outages
- Enabling timeouts, retries, and circuit breakers where needed
Authentication failures should degrade safely, not cascade.
Observability & Audit Readiness
Each authentication decision is a security event.
This design supports:
- Provider-level authentication metrics
- Token validation latency tracking
- Audit-friendly logging (without PII)
- Compliance readiness (SOC2, ISO, HIPAA)
If authentication cannot be observed, it cannot be secured.
Why Defaults Alone Are Not Enough
Spring Security defaults are excellent for:
- Single issuer
- Single token format
- Static authorization rules
Modern systems require:
- Multiple issuers at once
- Mixed token formats
- Provider-specific validation
- Centralized authorization logic
This architecture extends Spring Security without fighting the framework.

Conclusion
Modern authentication goes beyond simple token verification. It requires clearly defined trust boundaries, consistent validation strategies, and resilient system design. By implementing runtime authentication resolution along with provider-isolated validation, applications can safely accept tokens from multiple identity providers while maintaining clear separation of responsibilities.
When this approach is combined with unified RBAC enforcement, organizations gain a scalable security architecture that works equally well for startups and large enterprise platforms. The result is a flexible, future-ready system where security operates quietly in the background—remaining invisible when everything works and dependable when challenges arise.






























