As we see the advent of Healthtech, a question that every entrepreneur has in mind while building the platform is whether it is HIPAA compliant or not. While we do recommend having your software audited for compliance by an expert, here are some of the things that you can get done when you use AWS as a backend for any healthcare app.
To increase operational efficiency, a lot of businesses are using cloud providers like Amazon Web Services to manage their IT infrastructure. A huge number of healthcare providers today use the AWS cloud to store, process, and send protected health information (PHI) under HIPAA regulations.
HIPAA compliance in AWS creates a secure environment for the maintenance and retention of sensitive health information under this compliance. To start using AWS HIPAA-compliant cloud storage, a healthcare company must sign a HIPAA Business Associate Agreement (BAA) with AWS. It covers the security, control, and administrative processes mentioned in HIPAA.
AWS offers an extensive AWS HIPAA services list to develop scalable, secure, and fault-tolerant HIPAA solutions that can serve an unlimited number of healthcare use cases. In this article, we will cover aspects of building HIPAA-compliant software.
Start with AWS HIPAA Compliance
It’s very important to understand HIPAA compliance and the things that can go wrong if we don’t follow it properly. Check the list of fines/penalties imposed by authorities; one can see how much serious damage it can cause to your business if you don’t build your software correctly. Undoubtedly, building HIPAA-compliant software is one of the most important concepts for healthcare service providers.
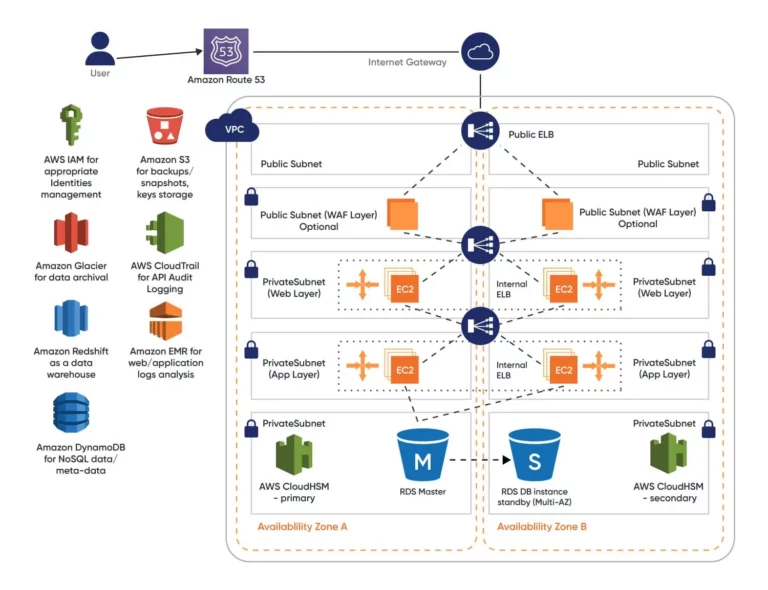
The major components of a 3 tier architecture of any software are the Client interface, Web or Mobile app, Server interface, APIs, and Database which stores the data. When it comes to HIPAA we have to make sure that all these 3 tiers are secured by following all best practices and guidelines provided by HIPAA.
Benefits of AWS for HIPAA Compliance
1. Built-in Security Tools
AWS offers strong built-in security tools that ensure data integrity, confidentiality, and compliance with stringent healthcare standards like HIPAA. These tools include AWS Identity and Access Management (IAM), encryption services, and logging that helps identify and address potential security incidents.
2. Scalability
The scalability of AWS infrastructure ensures that mental health solutions can grow with practice while maintaining compliance and performance. AWS enables you to scale infrastructure up or down based on demand. Pay-as-you-go pricing models allow organizations to scale cost-effectively, investing only in the resources they use. This flexibility is particularly beneficial for small to midsized practices looking to expand their digital capabilities without incurring excessive upfront costs.
3. Business Associate Agreement (BAA)
For healthcare organizations working on HIPAA-compliant projects, AWS offers BAAs, a critical component for ensuring compliance. The BAA establishes the shared responsibilities between your organization and AWS, ensuring that AWS services are used in a manner compliant with HIPAA regulations.
Free AWS Infrastructure Audit for Compliance and Optimization
Why Use AWS for HIPAA Compliance?
As far as operational and physical security are concerned, AWS has multiple layers to ensure the integrity and safety of customer data. But just using AWS services doesn’t ensure HIPAA compliance with your solution. When your AWS-based system deals with ePHI, you must follow the AWS HIPAA technical requirements and regulations.
The AWS HIPAA compliance efficiency is dependent on how it is used. AWS is building HIPAA compliant software with high-load systems that process vast amounts of ePHI under HIPAA. But, AWS only assumes responsibility for physical hardware security controls of a limited number of covered services listed here.
Shared Responsibility
AWS has a shared responsibility model to increase the total security level of Amazon’s cloud infrastructure.
Amazon handles managing infrastructure components and the physical security of the AWS data centers at different geographic locations. The AWS customers are responsible for the security and HIPAA-compliant architecture of cloud services that are being used. Let’s discuss the shared responsibility model in a more detailed manner. Here is a quick glance into the shared responsibility of Amazon and the Customer.
Amazon’s Responsibility
Amazon is in charge of the physical security of AWS cloud infrastructure. They manage the following areas:
- Computing
- Storage
- Databases
- Networking
- Regions
- Availability Zone
- Edge locations
Customer’s Responsibility
Customers are responsible for the security of AWS services being used and configured according to HIPAA-compliance solutions. Customers manage the security of the following areas
- Platform
- Applications
- Identity and access management tools and processes (IAM)
- Operating systems
- Networking traffic protection
- Firewall configurations
- Client and Server-side encryption
Guide for Implementing HIPAA-Compliant Software on AWS
1. Access Control
Access control plays an important part in any system; it is cloud-agnostic. As per HIPAA guidelines, our application should ensure that only authenticated users will be able to access the resources that are granted to them. AWS has a great service called IAM – Identity and Access Management which helps us grant specific access to specific users in easy steps.
IAM enables you to manage access to AWS services and resources securely. With its help, you can create and manage AWS users and groups and use permissions to allow and deny their access to AWS resources.
2. Disposal as a Requirement
Each account owner on AWS has the ability to install and configure retention for all services he uses, to prevent unnecessary data from being stored and to delete data from the service upon request, the application should give users a way to delete the data. Any company that collects health information must ensure it’s properly destroyed.
HIPAA requires that media have been cleared, purged, or destroyed consistent with NIST Special Publication 800-88, Guidelines for Media Sanitization, such that the PHI cannot be retrieved.
3. Data Backup and Storage
AWS Backup is a managed solution for the automatic backup of application data for all AWS services. It is a faster and easier backup solution for AWS customers. In the old era, backup and recovery were a nightmare, but AWS has made it pretty easy. It can be set up on a regular basis or carried out on request.
It also monitors the status of current backups and searches for and restores backups to ensure compliance with corporate and regulatory requirements. Most AWS services, like RDS, Elasticache, and S3 have native backup functionality.
Mindbowser Improved Performance of Rest APIs by 233% for A Healthcare Startup
6. Automatic Session Logouts
It’s really important to implement inactivity session logouts as per HIPAA guidelines. Using REST APIs along with frontend and backend combinations, one can easily implement the same. Though there is no global standard for timeout duration, It is important to understand that the risk of an “open” connection on an unattended workstation largely depends on the physical surroundings.
On an open floor in a hospital or in a busy emergency room accessible to the public, the risk is high, and the timeout should be shorter than 15 minutes.
Complete Guide for Complying with HIPAA Regulations
This guide aims to provide you with an understanding of the alterations that have occurred in HIPAA regulations as a result of the COVID-19 pandemic.

Conclusion
While AWS provides a foundation for building HIPAA-compliant telehealth platforms through its services like AWS HealthLake, AWS Comprehend Medical, and AWS IoT Medical Devices, it’s important to remember that these services alone do not guarantee full HIPAA compliance.
AWS and the telehealth provider share the responsibility for ensuring all aspects of HIPAA compliance are met. By implementing certain measures and leveraging the power of HIPAA compliance software, telehealth providers can effectively migrate risks, ensure data security, and maintain the patient trust while using AWS cloud services.
HIPAA Compliance refers to the set of rules and regulations established by the Health Insurance Portability and Accountability Act of 1996. It is crucial for healthcare software development to ensure the protection of sensitive patient data and maintain patient privacy.
AWS offers a wide range of services that can deliver a highly available, scalable, and secure application stack that can support a multitude of healthcare applications. It provides a HIPAA-eligible architecture that can support HIPAA-eligible, web-facing applications
AI can be used by healthcare organizations to aggregate and analyze health data to actively identify and prevent potential health issues, improving patient outcomes and reducing healthcare costs




















 BLOGS
BLOGS  NEWSROOM
NEWSROOM  CASE STUDIES
CASE STUDIES  WEBINARS
WEBINARS  PODCASTS
PODCASTS  ASSET HUB
ASSET HUB  EVENT CALENDAR
EVENT CALENDAR